Found this helpful? Share it with peers.
Introduction
Data sovereignty has evolved from a legal technicality into a cornerstone of operational resilience. What was once handed off to compliance teams and revisited only when regulations changed now sits at the center of how organizations manage risk and answer to regulators.
As IT ecosystems have grown more complex and fragmented, regulatory expectations have risen sharply — from merely protecting data to proving you control and own it at any time. For organizations in finance, healthcare, energy, and other critical infrastructure sectors, proving data ownership has become a direct factor in regulatory standing and operational resilience.
In this blog, we explore what data sovereignty actually means for regulated organizations, and why the deployment decisions that often feel like technical choices are in fact governance decisions.
Why Data Sovereignty Has Become a Strategic Priority
Several developments have pushed data sovereignty onto executive agendas, and understanding them helps explain why the topic now demands a more deliberate response.
Growing regulatory pressure on data control
Under NIS2 and DORA, regulators have moved from passive oversight to active verification. Sovereignty is now the primary evidence used to prove your organization maintains actual — not just contractual — accountability.
Increased cross-border data transfers and legal exposure
Every cross-border backup or vendor integration is a potential legal liability. In a fragmented global landscape, the cloud is no longer a borderless utopia — it is a complex map of conflicting legal reaches.
Cloud adoption raising jurisdictional questions
Cloud environments operate globally, but legal responsibility remains national or regional. Even if data is stored in a specific region, foreign access rights or ownership structures can lead to sovereignty issues.
Data sovereignty is the foundation of third-party risk management. Without it, your ability to respond to incidents or comply with audits is entirely dependent on a provider’s willingness and legal ability to cooperate.
What Data Sovereignty Really Means in Practice
At its core, data sovereignty is about legal authority: which jurisdiction’s laws apply to your data, regardless of where it sits.
This is frequently confused with two related but distinct concepts:
- Data residency refers to the physical location where data is stored.
- Data localization refers to legal requirements to store data within a specific jurisdiction.
Geography is not Sovereignty. Physical residency is a location; sovereignty is a power dynamic. True sovereignty means your data is immune to foreign jurisdictional overreach and remains under your exclusive operational control.
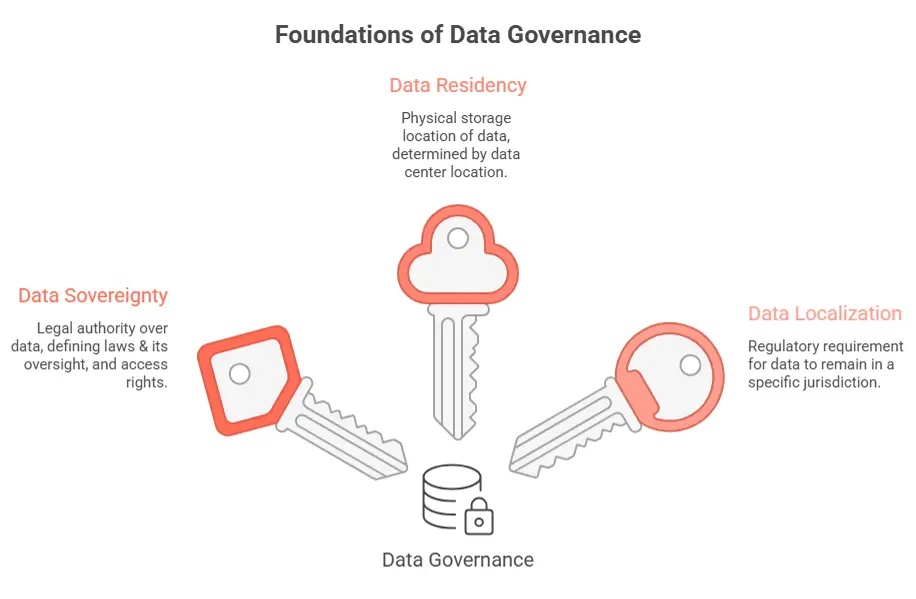
Data sovereignty defines legal responsibility for data, while data residency and localization describe where and how data must be stored
In practice, true control requires:
- Clear ownership and accountability structures
- Defined access rights and governance for privileged access
- Transparent audit trails
- Clarity in encryption and key management
- Contractual transparency regarding third-party involvement
Sovereignty is not a technical setting. It is a governance mandate that must link your infrastructure choices directly to your Risk Portfolio and Internal Controls (ICS) to ensure audit-readiness.
How Deployment Models Affect Data Sovereignty
Deployment architecture has a direct impact on sovereignty outcomes. Your choice of infrastructure model determines how much control your organization retains over its data, and how easily it can demonstrate that control to regulators.
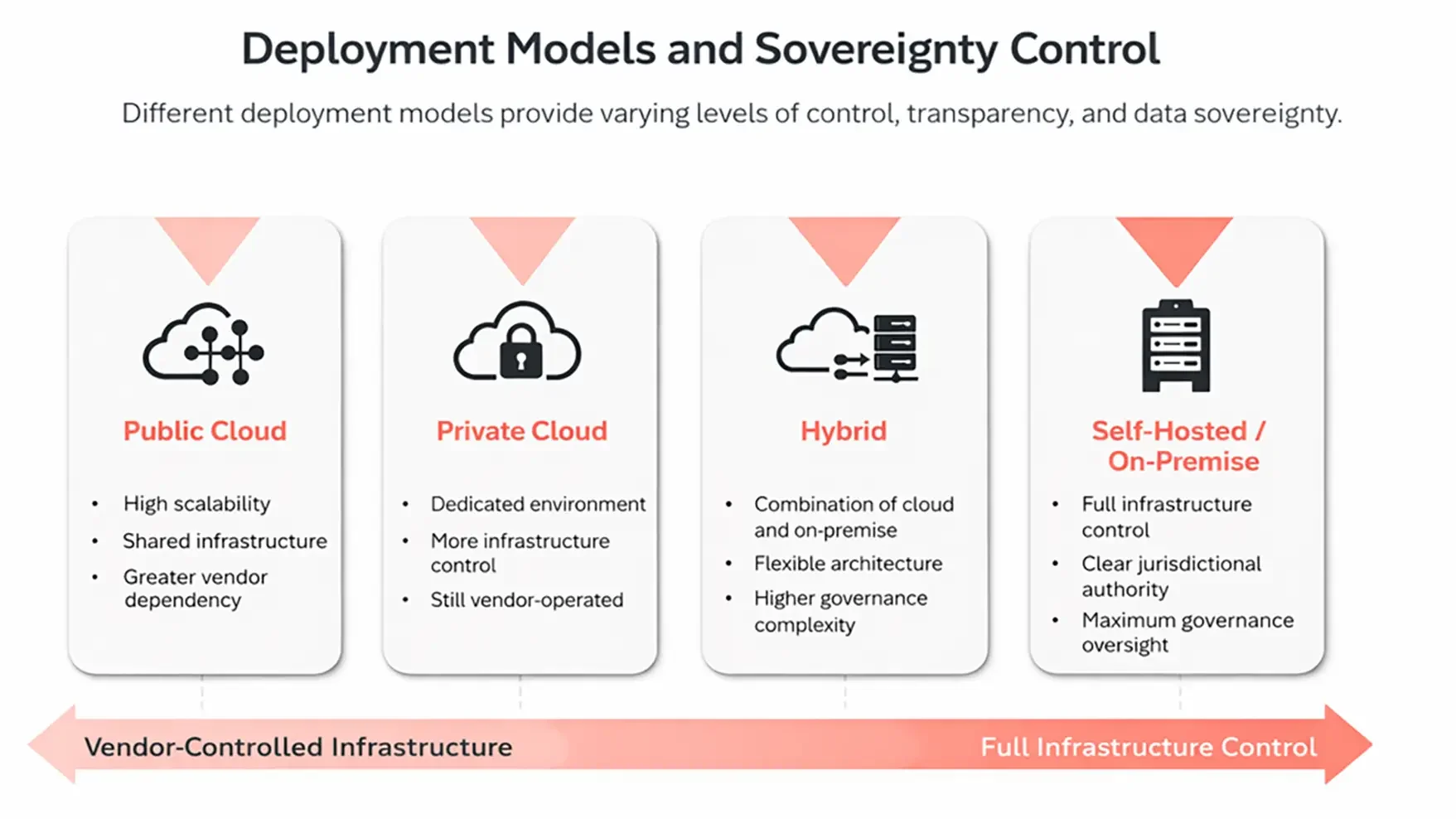
Deployment models influence how much control organizations retain over infrastructure, access, and data sovereignty
Public cloud
Public cloud environments offer scalability and advanced security features. However, they also entail the following:
- Shared responsibility models
- Complex subcontractor ecosystems
- Potential cross-border processing
- Increased dependence on vendor policies
Sovereignty in public cloud environments depends heavily on access controls, encryption models, and contract transparency.
Private cloud
Private clouds improve isolation and control, but many still involve third-party infrastructure providers. So, sovereignty depends on:
- The jurisdiction of the data center
- Governance for administrative access
- Audits rights and monitoring capabilities
Private cloud increases control, but does not eliminate governance obligations.
Hybrid environments
Hybrid models combine flexibility with complexity. Therefore, data flow between on-premise and cloud systems require:
- Consistent access management
- Centralized logging
- Clear assignment of responsibilities
- Coordinated incident response processes
Without this strong governance integration, hybrid setups could blur the lines of responsibility.
Self-hosted/on-premises
Self-hosted deployment provides the highest level of control over the infrastructure. Hence, organizations retain control over:
- Physical location
- Network segmentation
- Administrative access
- Monitoring and logging
For highly regulated industries, this model simplifies accountability and strengthens audit readiness.
Deployment Impact on Key Dimensions
Regardless of the architecture, deployment decisions shape several key aspects of data sovereignty:
- Jurisdictional authority
- What legal framework applies to stored and processed data and can this be clearly demonstrated to the supervisory authorities?
- Third-party exposure
- To what extent can providers, cloud providers, or subcontractors gain administrative or operational access to data?
- Regulatory accountability
- The ability to demonstrate oversights through structured controls, documentation and audit trails
- Incident transparency
- Full transparency regrading infrastructure, protocols, and processes in the event of security incidents or operational disruptions.
These factors are particularly relevant for the selection of company-wide systems. A GRC platform is the center of your organization’s compliance. Because it holds your most sensitive risk and control data, the deployment model you choose for it is the most critical sovereignty decision you will make.
Why Self-hosting Strengthens Regulatory Resilience
Sovereignty is a structural pillar. While not mandatory in all cases, self-hosting provides a Sovereignty-by-Design foundation, which offers numerous befits, such as:
Full control over infrastructure
Companies can specify exactly where data is stored and who has access to it.
Jurisdictional immunity
Keeping governance-critical systems within a more defined jurisdictional boundary can reduce conflicting legal claims.
Alignment with internal governance architecture
Self-hosted systems integrate seamlessly with established security frameworks, management structures and internal control environments.
Stability and independence
Organizations are less exposed to external political developments or shifting third-party conditions that could affect data access or contractual terms at short notice.
For institutions under continuous regulatory oversight, these advantages translate into clearer governance alignment and stronger audit readiness — not as a one-time benefit, but as a structural property of how the system is run.
How ADOGRC enables Sovereign and Secure Deployment
ADOGRC operationalizes data sovereignty through a deployment architecture built for regulated environments. Because GRC systems sit at the heart of business continuity, ADOGRC is fully containerized and deployable in three models:
- SaaS on dedicated EU infrastructure
- Private cloud in the customer’s chosen region
- On-premises behind the customer’s own firewall
This flexibility means organizations can determine exactly where data resides, who has administrative access, and how patches and updates are managed, turning sovereignty from a concept into a configurable reality.
Beyond infrastructure, ADOGRC builds sovereignty into daily operations. The platform links every risk, control, and compliance requirement to explicitly named owners. All changes, accesses, and reviews are logged in audit trails. When auditors ask who approved a control change, when, and based on what evidence, the answer is a single click.
By combining flexible deployment with structured, accountable workflows, ADOGRC ensures that data sovereignty is not an abstract concept you hope for, but a verifiable part of your GRC strategy.
Summary
Data sovereignty has outgrown its traditional owners in legal and IT departments. For heavily regulated organizations, it now touches every part of how risk is managed and how regulators are answered.
Getting the deployment model right is necessary, but it is not sufficient. Sovereignty must be built into how the organization operates day to day – into processes, controls, and the audit trail.
That is the gap GRC platforms like ADOGRC are designed to close. By combining deployment flexibility with structured governance workflows and auditable transparency, they enable organizations to demonstrate control, not just claim it.