Found this helpful? Share it with peers.
Introduction
Most end-user applications are born out of good intent. Someone notices that a task takes too long, that data is hard to combine, or that a report arrives too late to be useful. Instead of waiting for a formal solution, they build something themselves. The fix is small at first. A spreadsheet replaces a manual list. A macro removes a repetitive step. Sometimes a lightweight app connects data that otherwise never meets. None of this is planned as infrastructure — it is simply the fastest way to get the work done.
The interesting shift happens later. Other people notice the shortcut works and start using it. Then they adjust it slightly for their own case. Gradually, the tool stops belonging to one person, yet no one formally takes ownership. People trust the output because it has worked so far, not because anyone verified how it works.
At that point, the application already influences decisions while still being treated as a convenience. Knowledge about its logic sits with individuals, documentation exists only in fragments, and dependencies — a core concern of enterprise Architecture — are discovered only when something breaks.
That is where end-user computing (EUC) stops being just a productivity story and becomes a governance challenge.
When Helpful Becomes Invisible
After an end-user application leaves its creator, it gets adopted by colleagues who find it useful for their own work. One person copies a spreadsheet to adjust a calculation, another adapts it to handle slightly different data. As more people rely on the tool, it starts supporting work that matters to the organization, such as reporting, customer data handling, or financial calculations.
This wider adoption changes how the application is treated. Responsibility for maintaining it becomes unclear. Users assume the data is accurate, and no one checks whether the steps or formulas reflect the organization’s rules. Different teams may implement their own versions to solve similar problems, creating small inefficiencies and duplications that go unnoticed.
Because the application continues to produce results, these issues remain hidden until a problem arises — adding to the hidden costs of an unmanaged application portfolio. A miscalculation appears, a file is misplaced, or an audit requests details. At that point, several questions come up:
-
Who is responsible for maintaining this application?
-
Who understands how it works?
-
What data does it process?
-
How many people depend on it?
In many cases, no one can answer these questions fully.
Registration Is Not About Slowing People Down
When organizations introduce the idea of registering end-user applications, people often imagine complex forms, multiple approvals, and lengthy documentation. That perception alone can create resistance.
In reality, registration does not require documenting every detail of every tool. Its purpose is to create a shared understanding of what exists and who is responsible for it. By capturing this information, organizations gain the context they need to make informed decisions about security, investment, or system updates.
A registration process focuses on four key questions:
-
What applications exist in the organization?
-
Why does each application exist?
-
Who is responsible for maintaining and updating it?
-
How serious would the impact be if the application failed or contained errors?
Without answers to these questions, decisions rely on assumptions. Teams may duplicate effort, overlook risks, or delay improvements because no one has a clear view of the tools in use — exactly what Application Portfolio Management is designed to address. Registration does not stop people from creating solutions; it ensures that important tools are recognized and visible before they become critical to operations.
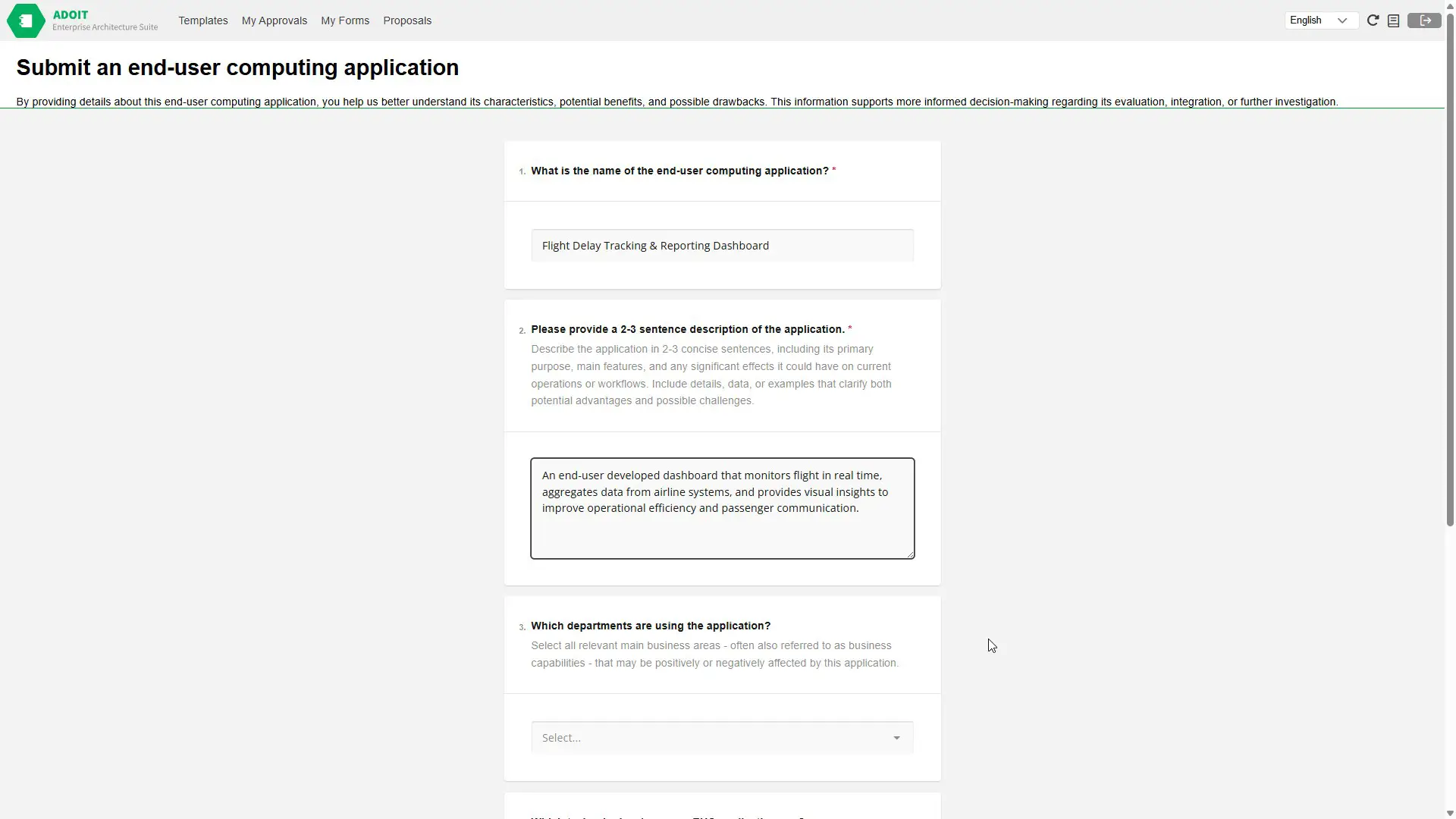
Make it easy for teams to register their tools with ADOIT Forms
From Control to Confidence
When organizations lack visibility into user-built tools, they usually compensate with blanket rules. Access gets restricted, identical policies are applied everywhere, and every application is reviewed with the same intensity. The intention is risk prevention, yet the effect is predictable: the lightweight tools people depend on for everyday work become harder to use than the problems they were created to solve. Innovation is not stopped, but it is treated as something suspicious by default.
Registration changes the situation because it replaces assumption with context. Once teams know which applications affect reporting, handle sensitive data, or support operational decisions, oversight can be directed instead of generalized. Some tools remain simple productivity aids and require little attention, while others justify testing, documentation, or defined ownership precisely because people rely on them.
The result is not stricter governance but more precise governance. Effort is spent where failure would matter, and routine work continues without unnecessary barriers. Registration therefore does not limit solution-building — it allows organizations to notice early which solutions quietly became operational dependencies.
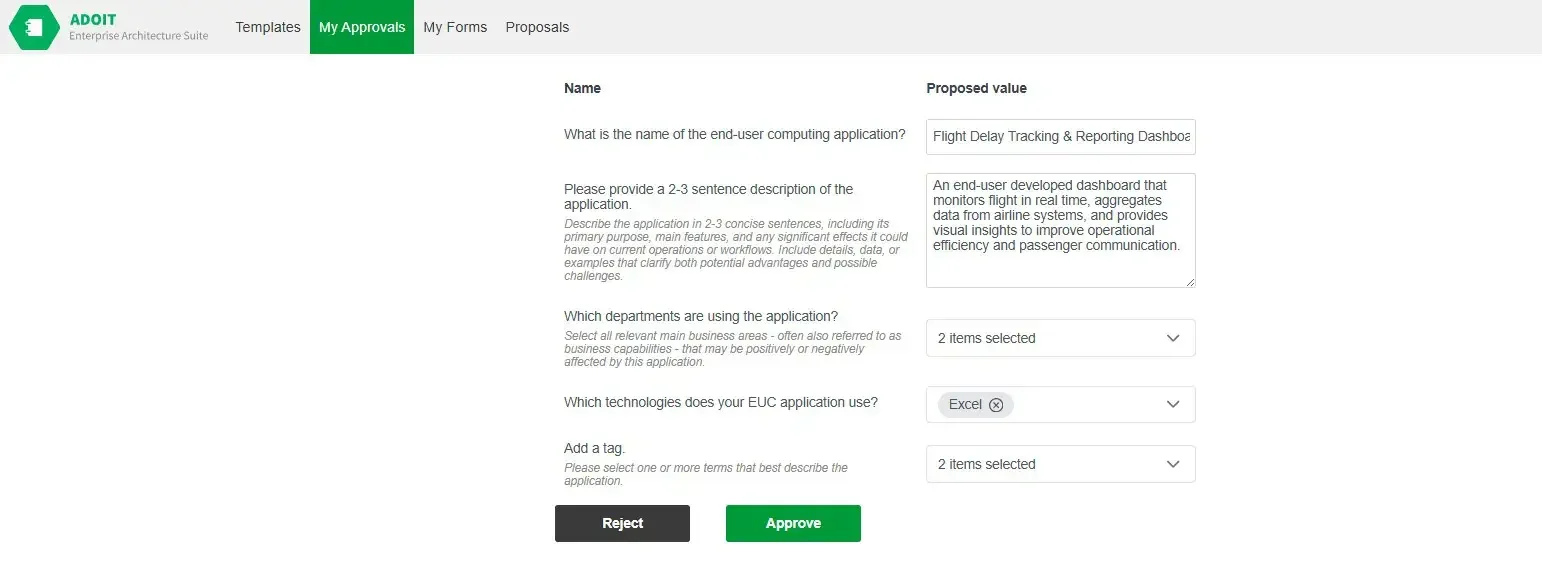
Stay in control of what gets used
Making the Invisible Visible
Most organizations already have a sense of what they wish they knew. After an incident or an audit request, someone inevitably says, we should have written that down somewhere. The challenge here is to capture the required information early, without interrupting the way people actually work.
The reaction people have to registration matters more than the form of information collection itself. If it resembles a control step that comes after the work is done, it gets postponed. If it appears at the moment someone shares a tool, updates it, or hands it over, it tends to be completed because it feels like part of the handover rather than an extra obligation. The difference is small in theory and significant in practice.
A workable process asks for only what helps others understand the tool later: who relies on it, what purpose it serves, and what could happen if it stops working. It does not attempt to validate the solution or interfere with how it was built. The goal is orientation, not approval.
When information is gathered in this way, people rarely experience it as governance. It feels closer to leaving notes for colleagues — a lightweight habit that prevents confusion later and allows operational decisions to rely on facts instead of reconstruction.
What Organizations Gain Over Time
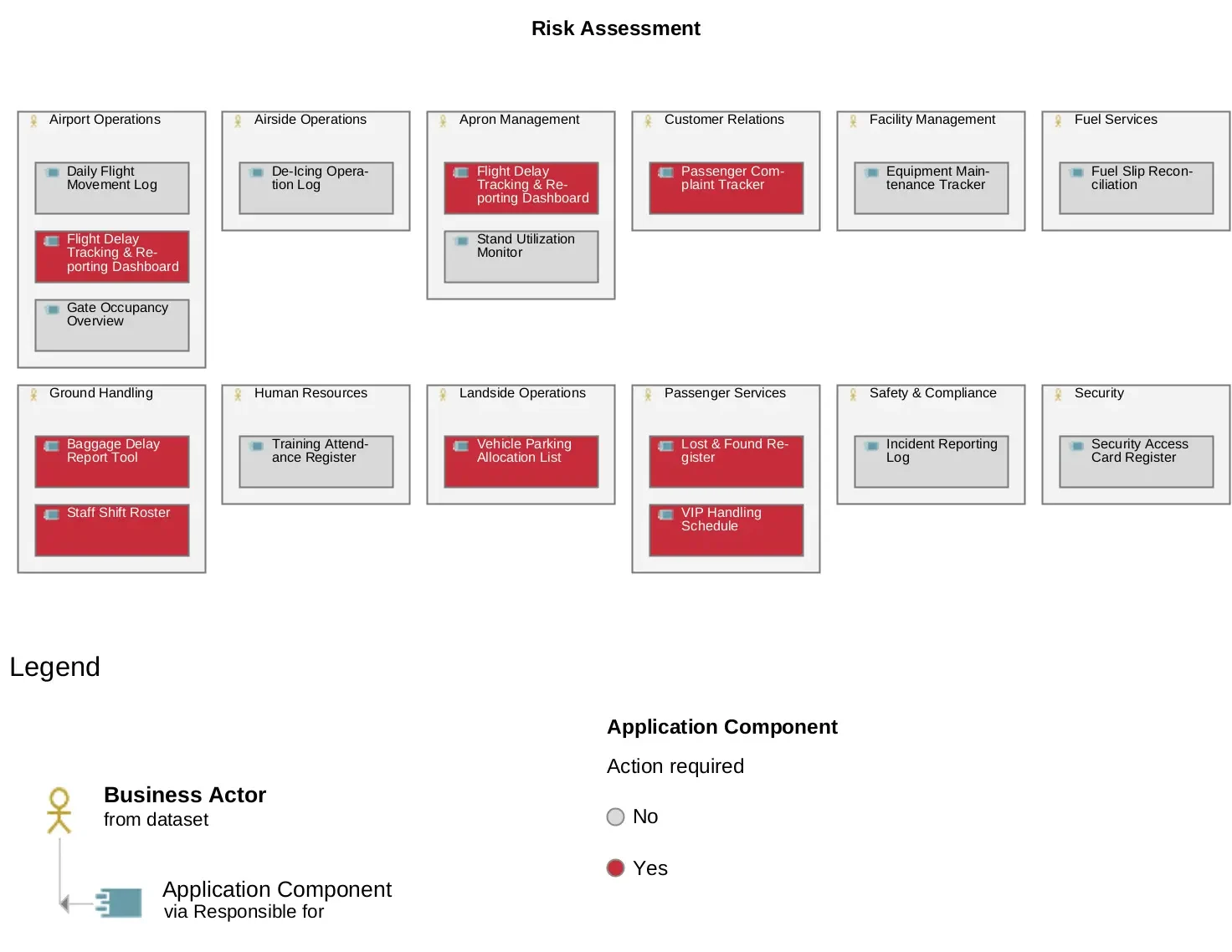
The benefits of EUC registration grow steadily. Initially, it provides visibility into which tools exist and who relies on them. As this information accumulates, it enables more informed decisions about security, resource allocation, and investment.
With a clear view of the application landscape — supported by an application portfolio assessment — patterns start to emerge. Teams notice when multiple versions of a similar tool appear, when risks are concentrated, or when costs build without oversight. Security and compliance efforts can focus on the areas that actually matter, while business leaders understand which innovations are reliable and supported by proper context.
The conversation within the organization shifts as well. Rather than responding only when problems arise, teams begin to ask forward-looking questions:
-
Which tools are becoming critical to operations?
-
Which tools require updates, replacement, or modernization?
-
Where does user-created innovation highlight unmet needs?
Spot risks before they impact the business
Summary
End-user applications are not an exception to the system landscape — they are part of how the landscape evolves. They appear where work moves faster than formal change cycles, and they often stay because they continue to solve a real problem.
The risk is therefore not their existence but their anonymity. As long as important tools remain unofficial, responsibility stays unclear and reactions happen only after impact becomes visible.
Registration addresses this at a practical level. It introduces awareness without redesigning the tool or interrupting the people using it. Once the organization recognizes which solutions others depend on, oversight becomes a matter of proportion rather than caution.
In that sense, EUC governance is less about restriction and more about timing: knowing early enough which small solutions have become part of operations.